Learn how to install FreeIPA on CentOS 8 with our detailed, step-by-step guide. Follow easy instructions to set up a robust identity management solution for centralized authentication, authorization, and account information. #centlinux #linux #freeipa
Table of Contents
What is FreeIPA?
FreeIPA is an open source and free software that provides a centrally managed IPA (Identity, Policy and Audit) system. FreeIPA uses a combination of 389 Directory Server, MIT Kerberos, NTP, DNS, IGC DogTag and other free open-source components.
FreeIPA is developed by Red Hat and distributed under GNU General Public License.
In this Lab, you will learn how to install FreeIPA server on CentOS 8, we will also configure a CentOS 8 client to use FreeIPA services.
Read Also: How to install FreeIPA on Rocky Linux 9

Components of FreeIPA Server
Core components of a FreeIPA server are.
- 389 Directory Server – LDAP implementation
- MIT Kerberos 5 – Authentication and Single Sign-On (SSO)
- Apache HTTP Server – For Web UI for FreeIPA
- DogTag – PKI certificate authority
- BIND – DNS server
- Chrony – NTP server
Linux Server Specification
We are using a CentOS 8 minimal installed virtual machine with following specification.
- CPU – 3.4 Ghz (2 cores)
- Memory – 2 GB
- Storage – 20 GB
- Operating System – CentOS Linux 8.0
- Hostname – freeipa-01.recipes.com
- IP Address – 192.168.116.206 /24
Installing FreeIPA on CentOS 8 requires a system with a minimum of 2GB RAM, a multi-core CPU, and at least 20GB of free disk space to accommodate the identity and authentication services comfortably. FreeIPA integrates several components such as LDAP, Kerberos, and DNS, so having reliable resources is important for smooth operation.
For testing or production environments, using a mini PC or a VPS is ideal. A VPS like Rose Hosting VPS offers dedicated Linux server resources and uptime, making it an excellent choice for setting up and managing FreeIPA without compromising your local machine’s performance.
[Limited Time Mini PC Offers – Click and Save!]
[Launch Your Own VPS with Rose Hosting – Click to Get Started!]
Disclaimer: This post contains affiliate links; using these links supports the blog at no extra cost to you.
Configure Static IP Address on CentOS 8
Connect with freeipa-01.recipes.com as root user by using a SSH tool.
This server is currently using a DHCP assigned IP Address. Configure network connection and manually assigned IP address, gateway and dns.
nmcli connection modify ens33 \
ipv4.method manual \
ipv4.address 192.168.116.206/24 \
ipv4.gateway 192.168.116.2 \
ipv4.dns 192.168.116.206Restart network connection to load changes.
nmcli connection down ens33 ; nmcli c up ens33Output:
Connection 'ens33' successfully deactivated (D-Bus active path: /org/freedesktop/NetworkManager/ActiveConnection/2)
Connection successfully activated (D-Bus active path: /org/freedesktop/NetworkManager/ActiveConnection/3)
Add an entry in local DNS resolver.
echo "192.168.116.206 freeipa-01.recipes.com freeipa-01" >> /etc/hostsInstall FreeIPA on CentOS 8
In CentOS 8, FreeIPA is available in AppStream repository, bundled in IDM module with different profiles to install according to sysadmins’ requirements.
We are installing selective profiles required to configure the FreeIPA server.
dnf module install -y idm:DL1/{server,client,dns,adtrust}FreeIPA server and related packages have been installed on our CentOS 8 server. Now we have to configure the FreeIPA installation according to our requirement.
ipa-server-install \
--unattended \
--realm RECIPES.COM \
--ds-password Ahmer@1234 \
--admin-password Ahmer@1234 \
--setup-dns \
--auto-reverse \
--forwarder 192.168.116.2Output:
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.8.0
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure DNS (bind)
* Configure the KDC to enable PKINIT
Warning: skipping DNS resolution of host freeipa-01.recipes.com
The domain name has been determined based on the host name.
Checking DNS domain recipes.com., please wait ...
DNS check for domain recipes.com. failed: The DNS operation timed out after 30.00042724609375 seconds.
Checking DNS forwarders, please wait ...
DNS server 192.168.116.2 does not support DNSSEC: answer to query '. SOA' is missing DNSSEC signatures (no RRSIG data)
Please fix forwarder configuration to enable DNSSEC support.
(For BIND 9 add directive "dnssec-enable yes;" to "options {}")
DNS server 192.168.116.2: answer to query '. SOA' is missing DNSSEC signatures (no RRSIG data)
Please fix forwarder configuration to enable DNSSEC support.
(For BIND 9 add directive "dnssec-enable yes;" to "options {}")
WARNING: DNSSEC validation will be disabled
Checking DNS domain 116.168.192.in-addr.arpa., please wait ...
Reverse zone 116.168.192.in-addr.arpa. for IP address 192.168.116.206 already exists
The IPA Master Server will be configured with:
Hostname: freeipa-01.recipes.com
IP address(es): 192.168.116.206
Domain name: recipes.com
Realm name: RECIPES.COM
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=RECIPES.COM
Subject base: O=RECIPES.COM
Chaining: self-signed
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 192.168.116.2
Forward policy: only
Reverse zone(s): No reverse zone
Disabled p11-kit-proxy
Synchronizing time
No SRV records of NTP servers found and no NTP server or pool address was provided.
Using default chrony configuration.
Attempting to sync time with chronyc.
Process chronyc waitsync failed to sync time!
Unable to sync time with chrony server, assuming the time is in sync. Please check that 123 UDP port is opened, and any time server is on network.
Warning: IPA was unable to sync time with chrony!
Time synchronization is required for IPA to work correctly
Configuring directory server (dirsrv). Estimated time: 30 seconds
[1/44]: creating directory server instance
Starting installation...
Created symlink /etc/systemd/system/multi-user.target.wants/dirsrv@RECIPES-COM.service â /usr/lib/systemd/system/dirsrv@.service.
Opening SELinux policy "//etc/selinux/targeted/policy/policy.31"
Successfully opened SELinux policy "//etc/selinux/targeted/policy/policy.31"
Allocate local instance <class 'lib389.DirSrv'> with ldapi://%2fvar%2frun%2fslapd-RECIPES-COM.socket
[2/44]: configure autobind for root
[3/44]: stopping directory server
[4/44]: updating configuration in dse.ldif
[5/44]: starting directory server
[6/44]: adding default schema
[7/44]: enabling memberof plugin
[8/44]: enabling winsync plugin
[9/44]: configure password logging
[10/44]: configuring replication version plugin
[11/44]: enabling IPA enrollment plugin
[12/44]: configuring uniqueness plugin
[13/44]: configuring uuid plugin
[14/44]: configuring modrdn plugin
[15/44]: configuring DNS plugin
[16/44]: enabling entryUSN plugin
[17/44]: configuring lockout plugin
[18/44]: configuring topology plugin
[19/44]: creating indices
[20/44]: enabling referential integrity plugin
[21/44]: configuring certmap.conf
[22/44]: configure new location for managed entries
[23/44]: configure dirsrv ccache and keytab
[24/44]: enabling SASL mapping fallback
[25/44]: restarting directory server
[26/44]: adding sasl mappings to the directory
[27/44]: adding default layout
[28/44]: adding delegation layout
[29/44]: creating container for managed entries
[30/44]: configuring user private groups
[31/44]: configuring netgroups from hostgroups
[32/44]: creating default Sudo bind user
[33/44]: creating default Auto Member layout
[34/44]: adding range check plugin
[35/44]: creating default HBAC rule allow_all
[36/44]: adding entries for topology management
[37/44]: initializing group membership
[38/44]: adding master entry
[39/44]: initializing domain level
[40/44]: configuring Posix uid/gid generation
[41/44]: adding replication acis
[42/44]: activating sidgen plugin
[43/44]: activating extdom plugin
[44/44]: configuring directory to start on boot
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc)
[1/10]: adding kerberos container to the directory
[2/10]: configuring KDC
[3/10]: initialize kerberos container
[4/10]: adding default ACIs
[5/10]: creating a keytab for the directory
[6/10]: creating a keytab for the machine
[7/10]: adding the password extension to the directory
[8/10]: creating anonymous principal
[9/10]: starting the KDC
[10/10]: configuring KDC to start on boot
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa-custodia
[1/5]: Making sure custodia container exists
[2/5]: Generating ipa-custodia config file
[3/5]: Generating ipa-custodia keys
[4/5]: starting ipa-custodia
[5/5]: configuring ipa-custodia to start on boot
Done configuring ipa-custodia.
Configuring certificate server (pki-tomcatd). Estimated time: 3 minutes
[1/30]: configuring certificate server instance
[2/30]: Add ipa-pki-wait-running
[3/30]: reindex attributes
[4/30]: exporting Dogtag certificate store pin
[5/30]: stopping certificate server instance to update CS.cfg
[6/30]: backing up CS.cfg
[7/30]: disabling nonces
[8/30]: set up CRL publishing
[9/30]: enable PKIX certificate path discovery and validation
[10/30]: starting certificate server instance
[11/30]: configure certmonger for renewals
[12/30]: requesting RA certificate from CA
[13/30]: setting audit signing renewal to 2 years
[14/30]: restarting certificate server
[15/30]: publishing the CA certificate
[16/30]: adding RA agent as a trusted user
[17/30]: authorizing RA to modify profiles
[18/30]: authorizing RA to manage lightweight CAs
[19/30]: Ensure lightweight CAs container exists
[20/30]: configure certificate renewals
[21/30]: configure Server-Cert certificate renewal
[22/30]: Configure HTTP to proxy connections
[23/30]: restarting certificate server
[24/30]: updating IPA configuration
[25/30]: enabling CA instance
[26/30]: migrating certificate profiles to LDAP
[27/30]: importing IPA certificate profiles
[28/30]: adding default CA ACL
[29/30]: adding 'ipa' CA entry
[30/30]: configuring certmonger renewal for lightweight CAs
Done configuring certificate server (pki-tomcatd).
Configuring directory server (dirsrv)
[1/3]: configuring TLS for DS instance
[2/3]: adding CA certificate entry
[3/3]: restarting directory server
Done configuring directory server (dirsrv).
Configuring ipa-otpd
[1/2]: starting ipa-otpd
[2/2]: configuring ipa-otpd to start on boot
Done configuring ipa-otpd.
Configuring the web interface (httpd)
[1/21]: stopping httpd
[2/21]: backing up ssl.conf
[3/21]: disabling nss.conf
[4/21]: configuring mod_ssl certificate paths
[5/21]: setting mod_ssl protocol list
[6/21]: configuring mod_ssl log directory
[7/21]: disabling mod_ssl OCSP
[8/21]: adding URL rewriting rules
[9/21]: configuring httpd
Nothing to do for configure_httpd_wsgi_conf
[10/21]: setting up httpd keytab
[11/21]: configuring Gssproxy
[12/21]: setting up ssl
[13/21]: configure certmonger for renewals
[14/21]: publish CA cert
[15/21]: clean up any existing httpd ccaches
[16/21]: configuring SELinux for httpd
[17/21]: create KDC proxy config
[18/21]: enable KDC proxy
[19/21]: starting httpd
[20/21]: configuring httpd to start on boot
[21/21]: enabling oddjobd
Done configuring the web interface (httpd).
Configuring Kerberos KDC (krb5kdc)
[1/1]: installing X509 Certificate for PKINIT
Done configuring Kerberos KDC (krb5kdc).
Applying LDAP updates
Upgrading IPA:. Estimated time: 1 minute 30 seconds
[1/11]: stopping directory server
[2/11]: saving configuration
[3/11]: disabling listeners
[4/11]: enabling DS global lock
[5/11]: disabling Schema Compat
[6/11]: starting directory server
[7/11]: updating schema
[8/11]: upgrading server
[9/11]: stopping directory server
[10/11]: restoring configuration
[11/11]: starting directory server
Done.
Restarting the KDC
Configuring DNS (named)
[1/11]: generating rndc key file
[2/11]: adding DNS container
[3/11]: setting up our zone
[4/11]: setting up our own record
[5/11]: setting up records for other masters
[6/11]: adding NS record to the zones
[7/11]: setting up kerberos principal
[8/11]: setting up named.conf
[9/11]: setting up server configuration
[10/11]: configuring named to start on boot
[11/11]: changing resolv.conf to point to ourselves
Done configuring DNS (named).
Restarting the web server to pick up resolv.conf changes
Configuring DNS key synchronization service (ipa-dnskeysyncd)
[1/7]: checking status
[2/7]: setting up bind-dyndb-ldap working directory
[3/7]: setting up kerberos principal
[4/7]: setting up SoftHSM
[5/7]: adding DNSSEC containers
[6/7]: creating replica keys
[7/7]: configuring ipa-dnskeysyncd to start on boot
Done configuring DNS key synchronization service (ipa-dnskeysyncd).
Restarting ipa-dnskeysyncd
Restarting named
Updating DNS system records
Configuring client side components
This program will set up IPA client.
Version 4.8.0
Using existing certificate '/etc/ipa/ca.crt'.
Client hostname: freeipa-01.recipes.com
Realm: RECIPES.COM
DNS Domain: recipes.com
IPA Server: freeipa-01.recipes.com
BaseDN: dc=recipes,dc=com
Configured sudoers in /etc/authselect/user-nsswitch.conf
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
WARNING: The configuration pre-client installation is not managed by authselect and cannot be backed up. Uninstallation may not be able to revert to the original state.
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Configuring recipes.com as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
==============================================================================
Setup complete
Next steps:
1. You must make sure these network ports are open:
TCP Ports:
* 80, 443: HTTP/HTTPS
* 389, 636: LDAP/LDAPS
* 88, 464: kerberos
* 53: bind
UDP Ports:
* 88, 464: kerberos
* 53: bind
* 123: ntp
2. You can now obtain a kerberos ticket using the command: 'kinit admin'
This ticket will allow you to use the IPA tools (e.g., ipa user-add)
and the web user interface.
Be sure to back up the CA certificates stored in /root/cacert.p12
These files are required to create replicas. The password for these
files is the Directory Manager password
The ipa-server-install command was successful
Allow required service ports in CentOS 8 firewall.
firewall-cmd --permanent --add-service={http,https,ldap,ldaps,kerberos,dns,ntp}
firewall-cmd --reloadVerify status of FreeIPA Server components.
ipactl statusOutput:
Directory Service: RUNNING
krb5kdc Service: RUNNING
kadmin Service: RUNNING
named Service: RUNNING
httpd Service: RUNNING
ipa-custodia Service: RUNNING
pki-tomcatd Service: RUNNING
ipa-otpd Service: RUNNING
ipa-dnskeysyncd Service: RUNNING
ipa: INFO: The ipactl command was successful
Before starting administration of FreeIPA server, We need to acquire a Kerberos ticket.
kinit adminCheck list of available kerberos tickets.
klistOutput:
Ticket cache: KCM:0
Default principal: admin@RECIPES.COM
Valid starting Expires Service principal
02/07/2020 22:31:24 02/08/2020 22:31:17 krbtgt/RECIPES.COM@RECIPES.COM
You can see that, we have acquired a kerberos ticket for 24 hours.
Check FreeIPA existing configurations.
ipa config-showOutput:
Maximum username length: 32
Maximum hostname length: 64
Home directory base: /home
Default shell: /bin/sh
Default users group: ipausers
Default e-mail domain: recipes.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: FALSE
Certificate Subject base: O=RECIPES.COM
Password Expiration Notification (days): 4
Password plugin features: AllowNThash, KDC:Disable Last Success
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$sysadm_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
IPA masters: freeipa-01.recipes.com
IPA master capable of PKINIT: freeipa-01.recipes.com
IPA CA servers: freeipa-01.recipes.com
IPA CA renewal master: freeipa-01.recipes.com
IPA DNS servers: freeipa-01.recipes.com
Configure DNS Server settings
Allow zone transfer from local network.
ipa dnszone-mod --allow-transfer=192.168.116.0/24 recipes.comOutput:
Zone name: recipes.com.
Active zone: TRUE
Authoritative nameserver: freeipa-01.recipes.com.
Administrator e-mail address: hostmaster.recipes.com.
SOA serial: 1581348934
SOA refresh: 3600
SOA retry: 900
SOA expire: 1209600
SOA minimum: 3600
Allow query: any;
Allow transfer: 192.168.116.0/24;
Add MX (Mail Exchange) record in DNS server.
ipa dnsrecord-add recipes.com @ --mx-rec="0 mail-server.recipes.com"Output:
Record name: @
MX record: 0 mail-server.recipes.com
NS record: freeipa-01.recipes.com.
Export Users’ Home Directories by using NFS server
We need to install nfs-utils package to configure a NFS server. FreeIPA has already installed nfs-utils package as a dependency.
Enable and start nfs-server and rpcbind services.
systemctl enable --now nfs-server rpcbindAllow NFS server related ports in CentOS 8 firewall.
firewall-cmd --permanent --add-service={nfs,mountd,rpc-bind}
firewall-cmd --reloadCreate a directory to store FreeIPA users’ home directories.
mkdir /home/guestsExport users’ home directories.
echo '/home/guests 192.168.116.0/24(rw,sync,no_subtree_check,root_squash)' >> /etc/exports
exportfs -ravOutput:
exporting 192.168.116.0/24:/home/guests
Add NFS service in FreeIPA server.
ipa service-add nfs/freeipa-01.recipes.comOutput:
------------------------------------------------------
Added service "nfs/freeipa-01.recipes.com@RECIPES.COM"
------------------------------------------------------
Principal name: nfs/freeipa-01.recipes.com@RECIPES.COM
Principal alias: nfs/freeipa-01.recipes.com@RECIPES.COM
Managed by: freeipa-01.recipes.com
Execute kadmin.local command.
kadmin.localOutput:
Authenticating as principal admin/admin@RECIPES.COM with password.
kadmin.local:
Add entry in keytab.
ktadd nfs/freeipa-01.recipes.com
exitOutput:
Entry for principal nfs/freeipa-01.recipes.com with kvno 1, encryption type aes256-cts-hmac-sha1-96 added to keytab FILE:/etc/krb5.keytab.
Entry for principal nfs/freeipa-01.recipes.com with kvno 1, encryption type aes128-cts-hmac-sha1-96 added to keytab FILE:/etc/krb5.keytab.
Entry for principal nfs/freeipa-01.recipes.com with kvno 1, encryption type camellia128-cts-cmac added to keytab FILE:/etc/krb5.keytab.
Entry for principal nfs/freeipa-01.recipes.com with kvno 1, encryption type camellia256-cts-cmac added to keytab FILE:/etc/krb5.keytab.
Configure default home directory and shell for new FreeIPA users.
ipa config-mod --homedirectory=/home/guests --defaultshell=/bin/bashOutput:
Maximum username length: 32
Maximum hostname length: 64
Home directory base: /home/guests
Default shell: /bin/bash
Default users group: ipausers
Default e-mail domain: recipes.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: FALSE
Certificate Subject base: O=RECIPES.COM
Password Expiration Notification (days): 4
Password plugin features: AllowNThash, KDC:Disable Last Success
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$sysadm_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
IPA masters: freeipa-01.recipes.com
IPA master capable of PKINIT: freeipa-01.recipes.com
IPA CA servers: freeipa-01.recipes.com
IPA CA renewal master: freeipa-01.recipes.com
IPA DNS servers: freeipa-01.recipes.com
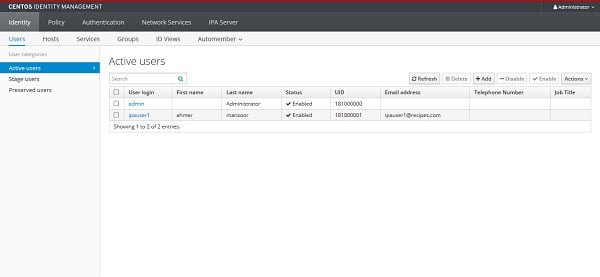
Create a FreeIPA user
Create a new FreeIPA user with the help of following command.
ipa user-add ipauser1 --first=ahmer --last=mansoor --passwordOutput:
Password:
Enter Password again to verify:
---------------------
Added user "ipauser1"
---------------------
User login: ipauser1
First name: ahmer
Last name: mansoor
Full name: ahmer mansoor
Display name: ahmer mansoor
Initials: am
Home directory: /home/guests/ipauser1
GECOS: ahmer mansoor
Login shell: /bin/bash
Principal name: ipauser1@RECIPES.COM
Principal alias: ipauser1@RECIPES.COM
User password expiration: 20200210162435Z
Email address: ipauser1@recipes.com
UID: 181000001
GID: 181000001
Password: True
Member of groups: ipausers
Kerberos keys available: True
Create home directory for FreeIPA user.
mkdir -m0750 -p /home/guests/ipauser1
chown 181000001:181000001 /home/guests/ipauser1Our FreeIPA setup has been completed successfully. Alternatively, you can perform administration of FreeIPA server by using the Web UI provided herewith.
Open URL http://freeipa-01.recipes.com in a browser.
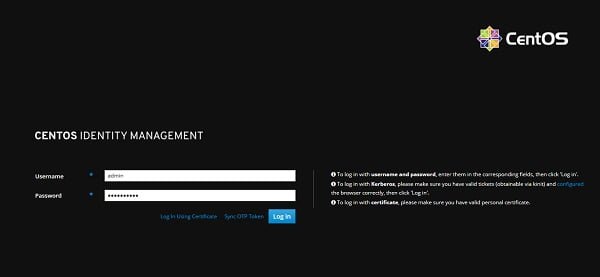
Login as admin user.
Add a CentOS 8 Client in FreeIPA Server
We are adding a CentOS 8 machine to FreeIPA server.
ipa host-add --ip-address 192.168.116.207 ipaclient.recipes.comOutput:
ipa: WARNING: The host was added but the DNS update failed with: DNS reverse zone 168.192.in-addr.arpa. for IP address 192.168.116.207 is not managed by this server
----------------------------------
Added host "ipaclient.recipes.com"
----------------------------------
Host name: ipaclient.recipes.com
Principal name: host/ipaclient.recipes.com@RECIPES.COM
Principal alias: host/ipaclient.recipes.com@RECIPES.COM
Password: False
Keytab: False
Managed by: ipaclient.recipes.com
Add our CentOS 8 machine in DNS server.
ipa dnsrecord-add recipes.com ipaclient --ttl=3600 --a-ip-address=192.168.116.207Output:
Record name: ipaclient
Time to live: 3600
A record: 192.168.116.207
Configure CentOS 8 machine as FreeIPA Client
To configure a CentOS 8 machine as FreeIPA client, we need to install following packages on it.
dnf module install -y idm:DL1/clientConfigure autofs to automatically mount the FreeIPA users’ home directory on ipaclient machine after successful login.
echo '* -rw 192.168.116.206:/home/guests/&' >> /etc/auto.guests
echo '/home/guests /etc/auto.guests' >> /etc/auto.masterEnable and start autofs service.
systemctl enable --now autofs.serviceAdd DNS server in network configurations of CentOS 8 client.
nmcli c m ens33 ipv4.dns 192.168.116.206
nmcli c down ens33 ; nmcli c up ens33Test DNS resolution by using dig command.
dig freeipa-01.recipes.comOutput:
; <<>> DiG 9.11.4-P2-RedHat-9.11.4-26.P2.el8 <<>> freeipa-01.recipes.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 31792
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
; COOKIE: f52733a39c74976ba8570e005e42d2172f9f5e5797eab7b3 (good)
;; QUESTION SECTION:
;freeipa-01.recipes.com. IN A
;; ANSWER SECTION:
freeipa-01.recipes.com. 1200 IN A 192.168.116.206
;; AUTHORITY SECTION:
recipes.com. 86400 IN NS freeipa-01.recipes.com.
;; Query time: 37 msec
;; SERVER: 192.168.116.206#53(192.168.116.206)
;; WHEN: Tue Feb 11 21:11:03 PKT 2020
;; MSG SIZE rcvd: 109
Configure CentOS 8 client by using ipa-client-install command.
ipa-client-install \
--enable-dns-updates \
--mkhomedir \
--ntp-server=192.168.116.206:323Output:
This program will set up IPA client.
Version 4.8.0
Discovery was successful!
Client hostname: ipaclient.recipes.com
Realm: RECIPES.COM
DNS Domain: recipes.com
IPA Server: freeipa-01.recipes.com
BaseDN: dc=recipes,dc=com
NTP server: 192.168.116.206:323
Continue to configure the system with these values? [no]: yes
Synchronizing time
Augeas failed to configure file /etc/chrony.conf
Using default chrony configuration.
Attempting to sync time with chronyc.
Time synchronization was successful.
User authorized to enroll computers: admin
Password for admin@RECIPES.COM:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=RECIPES.COM
Issuer: CN=Certificate Authority,O=RECIPES.COM
Valid From: 2020-02-06 18:32:37
Valid Until: 2040-02-06 18:32:37
Enrolled in IPA realm RECIPES.COM
Created /etc/ipa/default.conf
Configured sudoers in /etc/authselect/user-nsswitch.conf
Configured /etc/sssd/sssd.conf
Configured /etc/krb5.conf for IPA realm RECIPES.COM
Systemwide CA database updated.
Missing reverse record(s) for address(es): 192.168.116.207, fd15:4ba5:5a2b:1008:3d9b:4777:10ac:b523.
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config
Configuring recipes.com as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
Edit SSH configurations to use our FreeIPA service.
vi /etc/ssh/sshd_configFind and set following directives in this file.
KerberosAuthentication no
UsePAM yesRestart sshd.service to apply changes.
systemctl restart sshd.serviceNow login as ipauser1.
su - ipauser1Check User mount.
mount | grep /ipauser1Output:
192.168.116.206:/home/guests/ipauser1 on /home/guests/ipauser1 type nfs4 (rw,relatime,vers=4.2,rsize=262144,wsize=262144,namlen=255,hard,proto=tcp,timeo=600,retrans=2,sec=sys,clientaddr=192.168.116.207,local_lock=none,addr=192.168.116.206)
You can see that the home directory for user ipauser1 has been mounted by autofs service.
We have successfully install FreeIPA on CentOS 8 and configured a client to use Domain services.
Final Thoughts
Installing FreeIPA on CentOS 8 is a fantastic way to establish a centralized identity management solution for your network. With the right setup, you can streamline authentication, enhance security, and manage user permissions effectively.
Need a dependable Linux system administrator? I specialize in managing, optimizing, and securing Linux servers to keep your operations running flawlessly. Check out my services!
Feel free to reach out if you have any questions or need additional support!
FAQs
1. What are the prerequisites for installing FreeIPA on CentOS 8?
You need a CentOS 8 server with a static IP, fully qualified domain name (FQDN) set, root access, and updated system packages. Also ensure network connectivity and proper DNS configuration.
2. How do I enable the repository required for FreeIPA installation on CentOS 8?
Enable the idm:DL1 module with the command
dnf module enable idm:DL1
then synchronize repositories using
dnf distro-sync
before installing FreeIPA packages.
3. What command installs the FreeIPA server and its DNS components?
Run
dnf install ipa-server ipa-server-dns -y
to install the FreeIPA server along with DNS support packages.
4. How do I configure and set up the FreeIPA server after installation?
Execute
ipa-server-install
and follow the interactive prompts to configure hostname, domain, admin password, and optional integrated DNS and NTP settings.
5. How do I open the necessary firewall ports for FreeIPA on CentOS 8?
Use
firewall-cmd --permanent --add-service={ntp,http,https,ldap,ldaps,kerberos,kpasswd,dns}
firewall-cmd --reload
to allow FreeIPA network traffic through the firewall.
Recommended Courses
If you’re serious about building a career in IT, the Complete Linux Training Course to Get Your Dream IT Job 2025 by Imran Afzal is one of the best investments you can make in yourself. This highly rated course takes you from the basics of Linux to advanced system administration skills, preparing you for real-world IT roles and certifications.
Whether you’re a beginner or brushing up your skills, the structured lessons, hands-on labs, and career-oriented approach make it a perfect choice to boost your confidence and job readiness. Enroll now and start your Linux journey today!
Disclaimer: This post contains affiliate links. If you purchase through these links, I may earn a small commission at no additional cost to you. This helps support the site and allows me to continue creating valuable content.


Leave a Reply
You must be logged in to post a comment.