Learn how to install Gitea on Rocky Linux 10 with our step-by-step guide. Set up your own lightweight Git server, boost team collaboration, and secure your code today—don’t miss out on owning your projects with full control! #centlinux #linux #gitea
Table of Contents
Introduction
What is Gitea?
Gitea is a lightweight, self-hosted Git service written in Go. It allows developers and teams to manage Git repositories without relying on third-party platforms like GitHub or GitLab. Think of it as your private GitHub running on your own server. Since it’s open-source, you get full control over your repositories, user accounts, and data without worrying about vendor lock-in. Its minimal resource requirements make it perfect for small to medium teams or even individual developers who want autonomy over their code.
Unlike heavier alternatives, Gitea is designed to run smoothly on modest hardware. You don’t need enterprise-level servers to deploy it. Even a small VPS with 1 GB of RAM can host multiple repositories efficiently. This is a huge plus for startups and individuals who don’t want to spend heavily on infrastructure.
Moreover, Gitea’s simplicity is one of its biggest strengths. The installation process is straightforward, and the web interface is user-friendly. With built-in features like issue tracking, pull requests, and wiki support, it provides a complete development collaboration platform. If you’ve ever felt GitLab was too heavy or GitHub too restrictive, Gitea strikes the perfect balance.

Why Choose Gitea Over Other Git Platforms?
There are several Git hosting platforms available today, but Gitea stands out for a number of reasons:
- Lightweight & Fast – Unlike GitLab, which requires significant resources, Gitea is optimized to run on smaller servers.
- Easy Installation – You can set it up with just a few commands, and updates are simple to apply.
- Full Control – Since it’s self-hosted, you decide where your data lives. This is crucial for privacy and compliance requirements.
- Community-Driven – Gitea is open-source with contributions from developers worldwide, ensuring transparency and security.
- Low Maintenance – It doesn’t require constant tweaking or monitoring like heavier alternatives.
For teams looking for a reliable Git hosting solution without the overhead of enterprise tools, Gitea is an excellent choice.
Key Features of Gitea
Some of the core features that make Gitea appealing include:
- Repository Management: Create, clone, and manage Git repositories easily.
- User Management: Add users, assign permissions, and manage teams.
- Pull Requests & Code Review: Collaborators can propose changes and review code efficiently.
- Issue Tracking: A built-in system to track bugs, feature requests, and tasks.
- Wiki & Documentation: Each repository can have its own wiki for documentation.
- SSH & HTTPS Support: Secure ways to push and pull code.
- Integration Options: Supports webhooks and CI/CD integration.
- Cross-Platform: Runs on Linux, macOS, and Windows.
With these features, Gitea provides everything most teams need without unnecessary complexity.
If you’re serious about mastering version control and becoming confident with Git and GitHub, The Git & GitHub Bootcamp by Colt Steele is one of the best investments you can make in your tech career. This course is designed for beginners and professionals alike, covering everything from the basics of Git commands to advanced GitHub workflows that real developers use in collaborative environments.
Whether you’re preparing for a DevOps role, contributing to open-source projects, or simply improving your coding workflow, this bootcamp will give you practical, hands-on skills you can apply right away. [Enroll now through my affiliate link] and take the first step toward becoming a Git pro. (Disclaimer: This post contains affiliate links. If you make a purchase through these links, I may earn a small commission at no additional cost to you.)
Preparing Your Rocky Linux 10 Server
System Requirements for Gitea
Before jumping into installation, let’s check what’s needed to run Gitea efficiently. Since it’s lightweight, the requirements are modest compared to other Git hosting solutions:
- Operating System: Rocky Linux 10 (64-bit)
- CPU: 1 core (2+ recommended for larger teams)
- RAM: Minimum 1 GB (2 GB or more recommended)
- Storage: At least 10 GB free disk space (depends on repository size)
- Database: MariaDB, PostgreSQL, or SQLite
For small setups, SQLite can work just fine. But for production environments, MariaDB or PostgreSQL is recommended to ensure better performance and scalability.
One key advantage of Gitea is that it doesn’t need a high-end server. A simple VPS or even a Raspberry Pi can handle it for small projects. However, if you’re running an organization with hundreds of repositories, you’ll want to allocate more resources for smooth performance.
Recommended Hardware for Running Gitea
- Raspberry Pi 4 Model B – Perfect for lightweight self-hosted Git servers. Check Price on Amazon
- Samsung T7 Portable SSD – Fast external storage for backups and repositories. View on Amazon
- Synology 2-Bay DiskStation DS223j (Diskless) – Reliable storage solution for automated Git backups. See Latest Price
- APC Back-UPS 1500VA – Protects your Gitea server from power outages. Buy Now
💡 Tip: Investing in reliable hardware ensures your Gitea server runs smoothly and securely.
Updating and Securing Your Server
Before installation, ensure your Rocky Linux 10 system is updated and secure. Run the following commands:
sudo dnf update -y
sudo dnf upgrade -yIt’s also important to enable the firewall and allow necessary ports:
sudo firewall-cmd --permanent --add-service=http
sudo firewall-cmd --permanent --add-service=https
sudo firewall-cmd --reloadAdditionally, set up SELinux properly if it’s enforcing mode, as it can block some Gitea services. Security should always be your first priority before hosting any application that will be exposed to the internet.
Creating a Dedicated User for Gitea
Running services as root is a bad practice from a security perspective. Instead, we’ll create a dedicated user for Gitea:
sudo adduser --system --shell /bin/bash --comment 'Git Version Control' --create-home --home-dir /home/git gitThis ensures Gitea runs under a restricted user account, minimizing security risks in case of vulnerabilities. We’ll later assign ownership of Gitea files and directories to this user.
Installing Required Dependencies
Installing Git and Other Essential Packages
Since Gitea is a Git service, the first requirement is having Git installed on the system. Run the following command:
sudo dnf install git wget nano -yHere’s a quick breakdown:
- Git – Required for repository management.
- Wget – Used to download Gitea binary.
- Nano – A lightweight text editor for configuration files.
Without Git installed, Gitea won’t function, so this step is essential.
Setting Up MariaDB/PostgreSQL for Gitea
Gitea supports multiple databases, but MariaDB and PostgreSQL are the most popular choices. For simplicity, let’s go with MariaDB:
sudo dnf install mariadb-server -y
sudo systemctl enable mariadb --nowAfter installing MariaDB, run the secure installation script:
sudo mysql_secure_installationThis allows you to set a root password, remove anonymous users, and secure your database.
Configuring Database for Gitea
Once MariaDB is running, create a new database and user for Gitea:
CREATE DATABASE gitea CHARACTER SET 'utf8mb4' COLLATE 'utf8mb4_unicode_ci';
CREATE USER 'gitea'@'localhost' IDENTIFIED BY 'StrongPassword';
GRANT ALL PRIVILEGES ON gitea.* TO 'gitea'@'localhost';
FLUSH PRIVILEGES;Replace StrongPassword with a secure password. This database will be used later during the Gitea web setup.
Read Also: How to Install MATLAB on Rocky Linux 10
Downloading and Installing Gitea
Fetching the Latest Gitea Release
To install Gitea, download the latest stable release from the official Gitea site:
wget -O /tmp/gitea https://dl.gitea.io/gitea/1.21.7/gitea-1.21.7-linux-amd64(Replace 1.21.7 with the latest version available.)
Once downloaded, move it to the correct location:
sudo mv /tmp/gitea /usr/local/bin/
sudo chmod +x /usr/local/bin/giteaInstalling Gitea Binary
After moving the binary, verify the installation:
gitea --versionIf everything is correct, you should see the installed version displayed.
Setting Correct File Permissions
Now let’s create the necessary directories and assign permissions:
sudo mkdir -p /var/lib/gitea/{custom,data,log}
sudo chown -R git:git /var/lib/gitea/
sudo chmod -R 750 /var/lib/gitea/
sudo mkdir /etc/gitea
sudo chown root:git /etc/gitea
sudo chmod 770 /etc/giteaThese directories will store configurations, repositories, and logs. Proper permissions ensure that only the Gitea user has access, maintaining security.
Configuring Gitea as a Service
Creating a Systemd Service File for Gitea
To manage Gitea as a service, create a systemd service file:
sudo nano /etc/systemd/system/gitea.servicePaste the following:
[Unit]
Description=Gitea (Git with a cup of tea)
After=syslog.target
After=network.target
After=mariadb.service
[Service]
RestartSec=2s
Type=simple
User=git
Group=git
WorkingDirectory=/var/lib/gitea/
ExecStart=/usr/local/bin/gitea web --config /etc/gitea/app.ini
Restart=always
Environment=USER=git HOME=/home/git GITEA_WORK_DIR=/var/lib/gitea
[Install]
WantedBy=multi-user.targetStarting and Enabling Gitea Service
Reload systemd and start the service:
sudo systemctl daemon-reload
sudo systemctl enable gitea --nowVerifying the Service Status
Check the status:
sudo systemctl status giteaIf it’s running properly, Gitea will now be accessible at http://your-server-ip:3000.
Setting Up Reverse Proxy with Nginx
Installing and Configuring Nginx
By default, Gitea runs on port 3000, but it’s not practical to expose that directly to users. Instead, we’ll use Nginx as a reverse proxy to handle traffic on ports 80 (HTTP) and 443 (HTTPS). First, install Nginx:
sudo dnf install nginx -y
sudo systemctl enable nginx --nowNow create a configuration file for Gitea:
sudo nano /etc/nginx/conf.d/gitea.confAdd the following configuration:
server {
listen 80;
server_name gitea.example.com;
location / {
proxy_pass http://localhost:3000;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_set_header Host $host;
}
}Replace gitea.example.com with your domain name. After saving, test and restart Nginx:
sudo nginx -t
sudo systemctl restart nginxAt this point, you should be able to access Gitea via your domain without needing :3000.
Securing Gitea with SSL Certificates (Let’s Encrypt)
To enable HTTPS, we’ll use Certbot to generate free SSL certificates from Let’s Encrypt:
sudo dnf install certbot python3-certbot-nginx -y
sudo certbot --nginx -d gitea.example.comFollow the prompts to obtain and apply the certificate. Certbot will automatically configure SSL in Nginx and set up auto-renewal.
Now Gitea will be accessible securely via https://gitea.example.com.
Adjusting Firewall Rules
If you’re using Rocky Linux firewall, allow HTTP and HTTPS traffic:
sudo firewall-cmd --permanent --add-service=http
sudo firewall-cmd --permanent --add-service=https
sudo firewall-cmd --reloadThis ensures external users can access your Gitea instance over the internet.
Accessing Gitea Web Interface
First-Time Setup Wizard
With the reverse proxy and SSL in place, open your browser and visit:
https://gitea.example.comYou’ll see the Gitea Installation Wizard, where you’ll configure the application.
Configuring Database and Repository Path
Here’s what you need to enter in the setup form:
- Database Type: MySQL/MariaDB (or PostgreSQL if you used that).
- Host:
127.0.0.1:3306(for MariaDB). - Database Name:
gitea. - Username:
gitea. - Password: The password you created earlier.
Next, set repository paths:
- Repository Root Path:
/var/lib/gitea/data - Log Path:
/var/lib/gitea/log - Application Data Path:
/var/lib/gitea/data
These must match the directories created earlier.
Creating the First Admin User
Scroll down to the “Administrator Account Settings” section. Create your first admin user by filling out:
- Username: Choose a unique admin username.
- Password: Strong password for security.
- Email Address: A valid email for password resets.
Finally, click Install Gitea. The service will initialize, and you’ll be redirected to the login page.
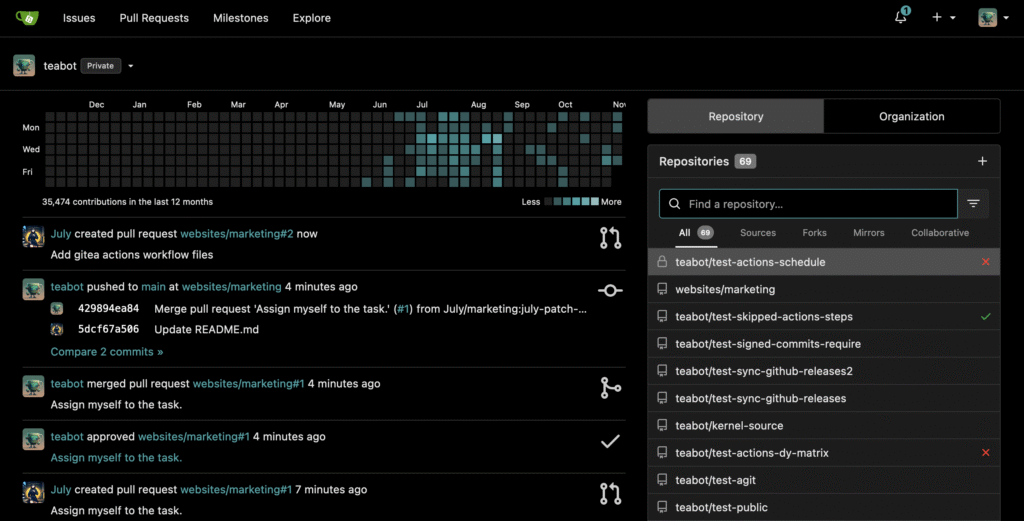
After successful you will be redirected to Gitea web interface.
Post-Installation Configuration
Enabling Email Notifications
For features like password resets, invitations, and notifications, configure SMTP. Edit Gitea’s config file:
sudo nano /etc/gitea/app.iniAdd the following under the [mailer] section:
[mailer]
ENABLED = true
FROM = "Gitea <noreply@gitea.example.com>"
MAILER_TYPE = smtp
HOST = smtp.yourmailserver.com:587
USER = noreply@gitea.example.com
PASSWD = your-email-passwordSave and restart Gitea:
sudo systemctl restart giteaNow email notifications will work properly.
Setting Up SSH for Git Operations
By default, users can clone via HTTPS, but SSH is more secure and widely preferred. Ensure sshd is running:
sudo systemctl status sshdIf not, enable it:
sudo systemctl enable sshd --nowGitea automatically detects SSH keys added to user accounts. Users just need to add their SSH public key in their profile, and they can push/pull using SSH URLs.
Customizing Gitea Configurations
The app.ini file allows extensive customization, including:
- Default branch name (e.g.,
maininstead ofmaster). - User registration settings (open, restricted, or disabled).
- Attachment and file size limits.
- OAuth integration for login (Google, GitHub, etc.).
After modifying the config file, always restart Gitea to apply changes.
Managing Users and Repositories
Adding and Managing Users
Admins can create new users or allow self-registration (if enabled). You can control this from Admin Panel → Users. Each user has a profile with SSH keys, email preferences, and repository settings.
For larger organizations, you can create Teams and assign specific roles such as “read-only,” “write,” or “admin.”
Creating and Managing Repositories
Repositories can be created either by individual users or under organizations. From the dashboard, click New Repository and fill in details like repository name, visibility (public/private), and license templates.
Once created, you can:
- Clone via SSH or HTTPS.
- Enable/disable issue tracking and wiki.
- Add collaborators with different permissions.
Setting Permissions and Collaborations
Gitea makes it easy to manage permissions:
- Read: User can only view and clone.
- Write: User can push changes.
- Admin: User can change settings and manage collaborators.
Teams and organizations make collaboration structured, ensuring security and proper access control.
Backup and Restore Strategies
Backing Up Database and Repositories
To prevent data loss, you need a backup strategy. Back up both the database and repositories.
For MariaDB:
mysqldump -u root -p gitea > gitea-backup.sqlFor Gitea data:
sudo tar -czvf gitea-data-backup.tar.gz /var/lib/gitea/Automating Backups with Cron Jobs
Create a cron job for automatic backups:
crontab -eAdd:
0 2 * * * /usr/bin/mysqldump -u root -pYourPassword gitea > /backups/gitea-$(date +\%F).sqlThis runs a backup daily at 2 AM.
Restoring Gitea from Backup
To restore, import the SQL file:
mysql -u root -p gitea < gitea-backup.sqlAnd extract repository data:
sudo tar -xzvf gitea-data-backup.tar.gz -C /var/lib/gitea/This ensures you can recover from accidental deletions or server crashes.
Performance Tuning for Gitea
Optimizing Database Settings
Performance often comes down to how well the database is tuned. Since Gitea relies heavily on its database, tweaking MariaDB or PostgreSQL settings can make a big difference.
For MariaDB, open the configuration file:
sudo nano /etc/my.cnf.d/server.cnfRecommended changes:
[mysqld]
innodb_buffer_pool_size=512M
innodb_log_file_size=128M
max_connections=200
query_cache_type=1
query_cache_size=64M- innodb_buffer_pool_size should be set to 50–70% of your server’s RAM for best performance.
- query_cache helps speed up repeated queries, useful for frequently accessed repositories.
- max_connections prevents overload when many users connect simultaneously.
After editing, restart MariaDB:
sudo systemctl restart mariadbFor PostgreSQL, tweak parameters in /var/lib/pgsql/data/postgresql.conf. Adjust values like shared_buffers, work_mem, and max_connections depending on available system resources.
Caching Strategies for Better Performance
Caching can drastically reduce database load. Gitea supports using Redis as a cache backend.
Install Redis:
sudo dnf install redis -y
sudo systemctl enable redis --nowEdit Gitea’s config:
[cache]
ADAPTER=redis
HOST=127.0.0.1:6379Restart Gitea to apply changes. Redis ensures faster access to frequently used data, improving responsiveness.
Scaling Gitea for Larger Teams
If you’re planning to use Gitea for a large organization, consider:
- Load Balancing – Deploy multiple Gitea instances behind a load balancer.
- External Database – Run MariaDB/PostgreSQL on a dedicated server for better performance.
- Object Storage – Store repository files, attachments, and avatars in external storage like MinIO, AWS S3, or similar solutions.
- Monitoring – Use tools like Prometheus + Grafana to track CPU, memory, and database usage.
This ensures Gitea can handle hundreds of users and repositories without slowing down.
Common Issues and Troubleshooting
Fixing Database Connection Errors
One of the most common issues during setup is failing to connect to the database. If you see errors like:
[ERROR] Failed to connect to database: Access denied for user 'gitea'@'localhost'Check the following:
- Ensure MariaDB/PostgreSQL is running.
- Verify that the username and password in
app.iniare correct. - Confirm that the user has privileges on the database.
Run:
SHOW GRANTS FOR 'gitea'@'localhost';If permissions are missing, reapply the grants.
Resolving Permission Issues
Sometimes Gitea cannot write to its directories due to incorrect file permissions. This leads to errors like repository creation failures.
Check ownership:
ls -l /var/lib/gitea/If files are owned by root, fix with:
sudo chown -R git:git /var/lib/gitea/This ensures the Gitea user has proper access.
Checking Gitea Logs
Logs are your best friend when diagnosing issues. Logs are located in:
/var/lib/gitea/log/To view real-time logs:
tail -f /var/lib/gitea/log/gitea.logErrors here will usually point to missing configurations, permission problems, or database misconfigurations.
Keeping Gitea Up to Date
Updating Gitea Binary Safely
Keeping Gitea updated ensures you have the latest security patches and features. To update:
Stop the service:
sudo systemctl stop giteaDownload the latest binary:
wget -O /tmp/gitea https://dl.gitea.io/gitea/1.21.8/gitea-1.21.8-linux-amd64Replace the old binary:
sudo mv /tmp/gitea /usr/local/bin/ sudo chmod +x /usr/local/bin/giteaRestart the service:
sudo systemctl start giteaUpdating Dependencies
Don’t forget to keep your system packages and database up to date:
sudo dnf update -yFor MariaDB/PostgreSQL, apply updates as recommended by your distro.
Best Practices for Upgrades
- Always back up your database and repositories before upgrading.
- Test upgrades on a staging server before applying them to production.
- Read release notes to check for breaking changes.
By following these steps, you can safely keep Gitea updated with minimal downtime.
Alternative Installation Methods
Installing Gitea via Docker
Docker simplifies installation by encapsulating Gitea and its dependencies. Install Docker:
sudo dnf install docker-ce docker-ce-cli containerd.io -y
sudo systemctl enable docker --nowThen run Gitea:
docker run -d --name=gitea -p 3000:3000 -p 222:22 \
-v /var/lib/gitea:/data \
gitea/gitea:latestThis runs Gitea in a container with persistent storage in /var/lib/gitea.
Using Podman on Rocky Linux
Rocky Linux also supports Podman, a daemonless container engine:
sudo dnf install podman -yThen run:
podman run -d --name=gitea -p 3000:3000 -p 222:22 \
-v /var/lib/gitea:/data \
docker.io/gitea/gitea:latestPodman works without requiring a daemon like Docker, making it more secure in some environments.
Pros and Cons of Containerized Installation
Pros:
- Easier installation and upgrades.
- Consistent environment across servers.
- Isolated dependencies.
Cons:
- More complex networking setup.
- Requires container expertise.
- Performance overhead compared to native binary installation.
For small setups, installing Gitea directly on the host system is simpler. For larger, scalable deployments, Docker or Podman is the better choice.
Conclusion
Installing Gitea on Rocky Linux 10 gives you a powerful, lightweight, and flexible Git hosting solution. Whether you’re a solo developer or managing a team, Gitea provides all the essential features—repositories, issues, pull requests, wikis—without the heavy system requirements of GitLab or the vendor lock-in of GitHub.
We started by preparing the server, installing dependencies, setting up a database, downloading Gitea, and configuring it as a system service. Then, we secured it with Nginx and SSL, configured email and SSH, learned how to manage users and repositories, implemented backup strategies, tuned performance, and covered troubleshooting. Finally, we explored containerized deployments as an alternative.
With this guide, you’re ready to host your own private Git service on Rocky Linux 10 and enjoy full control over your code and collaboration environment. However, if you face any difficulty in Gitea configuration you can contact me.
FAQs
1. Is Gitea free to use?
Yes, Gitea is completely free and open-source. You can install, customize, and run it without licensing costs.
2. Can I migrate from GitHub/GitLab to Gitea?
Absolutely. Gitea supports repository import via Git clone, and you can also migrate issues, pull requests, and wiki data with built-in migration tools.
3. How do I enable HTTPS on Gitea?
The recommended way is using Nginx with Let’s Encrypt SSL certificates. Certbot automates the certificate installation and renewal.
4. What is the difference between Gitea and Gogs?
Gitea was forked from Gogs in 2016. While Gogs is still maintained, Gitea has a larger community, more frequent updates, and richer features.
5. Can Gitea handle enterprise-level projects?
Yes, with proper scaling strategies (load balancers, external databases, caching, object storage), Gitea can support large teams and thousands of repositories.

Leave a Reply
You must be logged in to post a comment.